Title: Unveiling the Mystery: What Do Cryptocurrency Hashes Look Like?
Introduction:
In this brief review, we will explore the positive aspects and benefits of understanding what cryptocurrency hashes look like. Cryptocurrency hashes play a crucial role in securing transactions and ensuring the integrity of blockchain networks. By comprehending their appearance and characteristics, individuals can gain a deeper understanding of the underlying technology and improve their overall cryptocurrency experience.
I. Understanding Cryptocurrency Hashes:
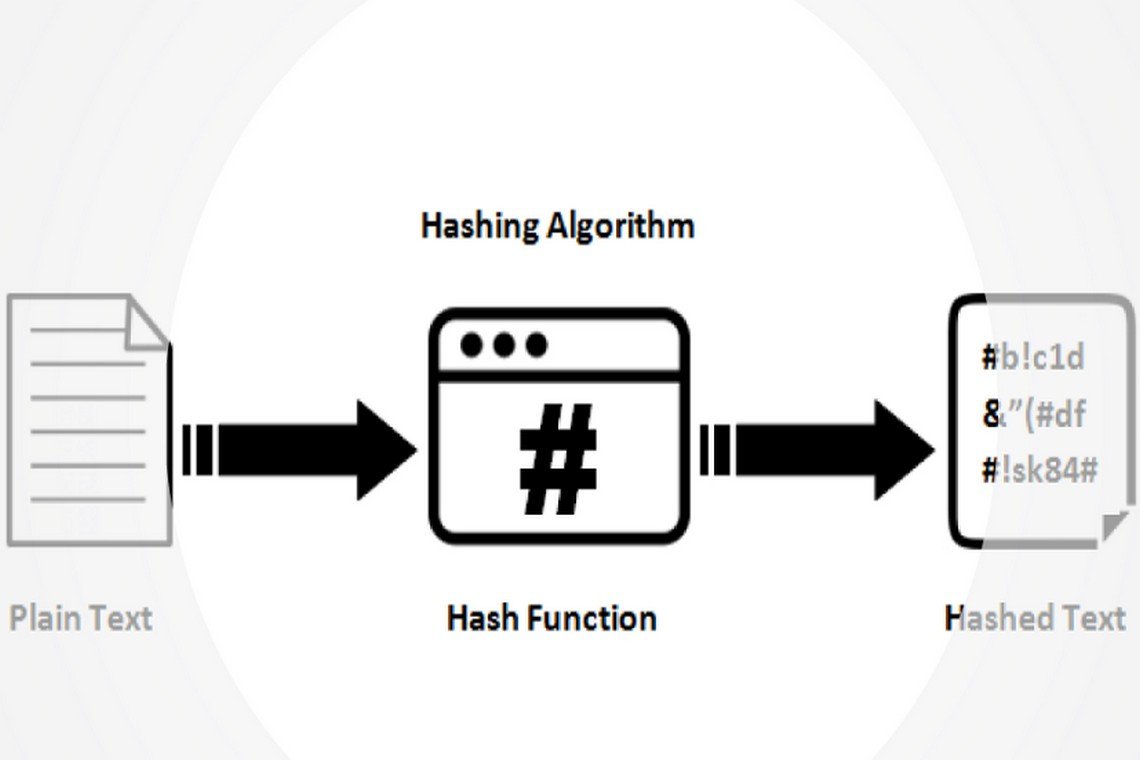
1. Definition: Cryptocurrency hashes are alphanumeric representations of data, generated through complex mathematical algorithms.
2. Appearance: Cryptocurrency hashes typically appear as a long string of random letters and numbers.
3. Fixed Length: Hashes have a consistent length, regardless of the size of the input data.
4. Unidirectional: It is virtually impossible to reverse-engineer the original data from a hash.
5. Unique: Even the slightest change in input data will produce a completely different hash.
II. Benefits of Understanding Cryptocurrency Hashes:
1. Enhanced Security: By comprehending cryptocurrency hashes, users can appreciate the robust security measures employed by blockchain networks. The uniqueness and fixed length of hashes make them highly resistant to tampering and fraud.
2. Verification of Data Integrity: Cryptocurrency hashes serve as digital fingerprints, allowing users
What data is hashed in blockchain?
Hashing in blockchain is a cryptographic process which takes an input (such as text) and turns it into an output of fixed length and structure known as the 'hash value'. It is always the same length and one-way, meaning it cannot be reversed.
What does it mean when data is hashed?
Hashing is the practice of transforming a given key or string of characters into another value for the purpose of security. Unlike standard encryption, hashing is always used for one-way encryption, and hashed values are very difficult to decode.
When should files be hashed?
Hashing has a large number of applications in cybersecurity, centering around the ability to verify that data is legitimate. With a secure hashing algorithm, one could verify that a downloaded file matched what was expected. In fact, many projects provide hashes alongside their downloads.
Does blockchain use encryption or hashing?
The most common use of cryptography is in the application and consensus layers of the blockchain. The hashing algorithm mainly helps to create block identity, ensure the integrity of the blockchain, and act as a key component of consensus algorithms such as Bitcoin's Proof of Work.
What is hashing in a blockchain?
In a cryptocurrency blockchain, a hash is a deterministic hexadecimal number. This means that no matter how many characters the input has, the hash will always be the same number of characters. For instance, Bitcoin's hashes are always 64 digits.

#Ethereum I'm going to make you understand things you previously didn't. I'm going to pull you out of ignorance and into knowledge. This will make you stronger. Front ends are just writing assistants. You want to freely associate and communicate with your peers by publishing…
— Richard Heart (@RichardHeartWin) November 25, 2023
How are hashes calculated?
Hashing involves applying a hashing algorithm to a data item, known as the hashing key, to create a hash value. Hashing algorithms take a large range of values (such as all possible strings or all possible files) and map them onto a smaller set of values (such as a 128 bit number).
Frequently Asked Questions
What is the formula for hash calculation?
With modular hashing, the hash function is simply h(k) = k mod m for some m (usually, the number of buckets). The value k is an integer hash code generated from the key. If m is a power of two (i.e., m=2p), then h(k) is just the p lowest-order bits of k.
What is meant by hashing algorithm?
Definition: A hash algorithm is a function that converts a data string into a numeric string output of fixed length. The output string is generally much smaller than the original data.
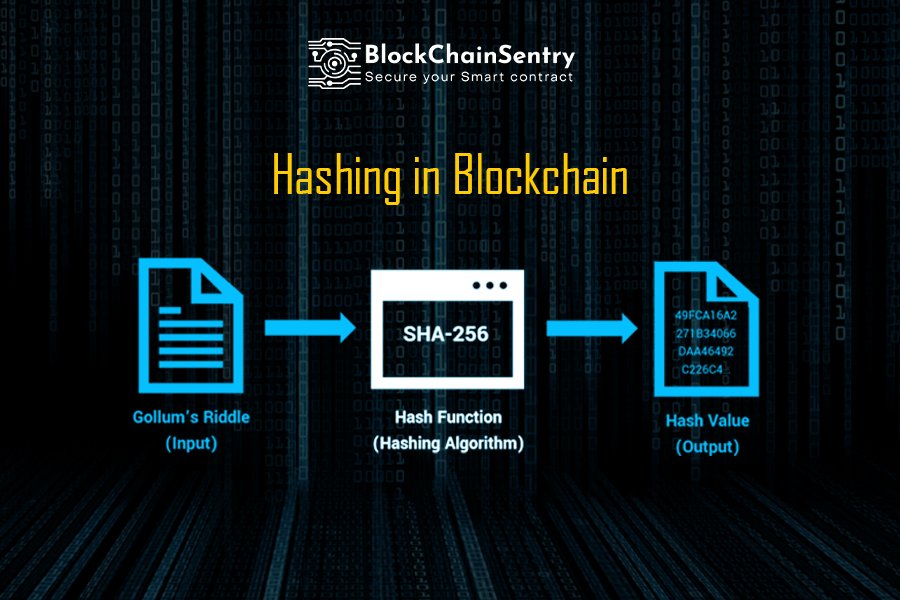
What is the best hashing algorithm for blockchain?
SHA-256
SHA-256 stands for Secure Hash Algorithm that generates a 256-bit digest of a message. This is one of the most renowned hashing algorithms used by several cryptocurrencies. Another popular application of this algorithm is Digital Signing Verification.
How does hash function work in blockchain?
A hash function turns an input (for example text) into a string of bytes with a fixed length and structure. The output or value created is called a 'hash value' or 'checksum. ' Any hash value created from data using a specific hashing algorithm is always the same length and one-way - it cannot be reversed.
How blockchain hash is calculated?
Solving a hash involves computing a proof-of-work, called a NONCE, or “number used once”, that, when added to the block, causes the block's hash to begin with a certain number of zeroes. Once a valid proof-of-work is discovered, the block is considered valid and can be added to the blockchain.
How does Hashrate work?
A hashrate is a measure of how many calculations can be performed per second and can be measured in billions, trillions, quadrillions, and quintillions. For example, a hashrate of 1TH/s means one trillion calculations can be performed every second. These calculations are being measured based on mining.
What is sha256 in blockchain?
The SHA-256 algorithm is a cryptographic hashing function used in the Bitcoin blockchain network to ensure the integrity of transactions and the security of the network as a whole. In the Bitcoin blockchain, transactions are collected into blocks, which are then added to the blockchain.
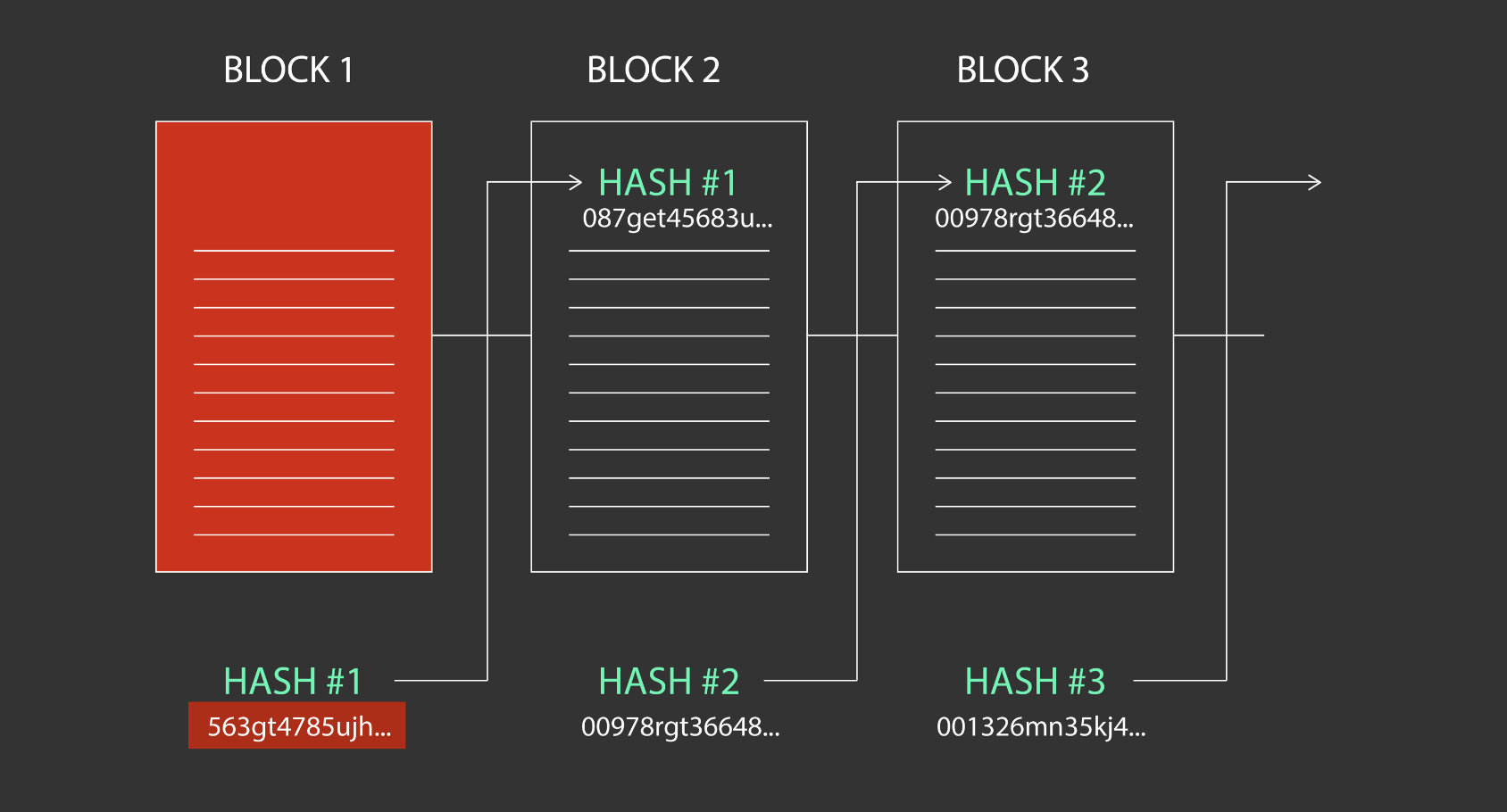
What is the block hash of the blockchain?
The block hash ensures the integrity and security of the blockchain by preventing tampering. It links blocks together in sequential order, forming a reliable transaction history. They play a vital role in maintaining the immutability and trustworthiness of the blockchain network.
Which hash function is blockchain?
SHA-256
A Bitcoin's blockchain uses SHA-256 (Secure Hash Algorithm) hashing algorithm. In 2001, SHA-256 Hashing algorithm was developed by the National Security Agency (NSA) in the USA.
FAQ
- What is the hash address of a blockchain?
- A transaction hash is a string of letters and numbers that is generated when a cryptocurrency transaction is initiated. It is a unique identifier that is used to track the transaction on the blockchain. Every transaction that occurs on the blockchain is recorded as a block, and each block has a unique hash.
- What is the block version of the blockchain?
- The block version indicates the set of validation rules to follow, while the previous block hash links the current block to the preceding one, forming the chain in the blockchain. The Merkle root is a data structure used to efficiently summarize all the transactions in the block.
- What is an example of a block hash?
- For example, 000000000019d6689c085ae165831e934ff763ae46a2a6c172b3f1b60a8ce26f is the block hash of the first bitcoin block ever created. The block hash identifies a block uniquely and unambiguously and can be independently derived by any node by simply hashing the block header.
- How to do hashing in blockchain?
- Blockchain Hash Function. A hash function takes an input string (numbers, alphabets, media files) of any length and transforms it into a fixed length. The fixed bit length can vary (like 32-bit or 64-bit or 128-bit or 256-bit) depending on the hash function which is being used. The fixed-length output is called a hash.
- How do you hash a transaction?
- Find a transaction using the asset's contract address
- Go to the ERC20 Token Txns tab.
- Select the Txn Hash that matches your transaction.
- Copy the Transaction Hash.
- How do I send a transaction to blockchain?
- In order to put a transaction on the blockchain, complete the following steps:
- Fill in the transaction fields.
- Sign transaction: generate sender's signature and add it to the transaction.
- Send transaction to a node.
- What is the hash 256 in blockchain?
- SHA-256 forms a critical component of major blockchain protocols like Bitcoin and Bitcoin SV. SHA-256 enables the proof-of-work (PoW) consensus algorithm on the Bitcoin blockchain. The cryptographic hash function is used to verify transactions on the blockchain protocol.
- What does each block in a blockchain contain the hash of?
- “Each block contains a hash (a digital fingerprint or unique identifier), timestamped batches of recent valid transactions, and the hash of the previous block.
- How does hash work?
- A hash function is a mathematical function or algorithm that simply takes a variable number of characters (called a ”message”) and converts it into a string with a fixed number of characters (called a hash value or simply, a hash).
Why is hashing used in blockchain
| What is an example of hashing? | Hashing is designed to solve the problem of needing to efficiently find or store an item in a collection. For example, if we have a list of 10,000 words of English and we want to check if a given word is in the list, it would be inefficient to successively compare the word with all 10,000 items until we find a match. | ||||||||||
| How many digits is a blockchain hash? | 64 symbols SHA-256 generates hashes that are 256 bits long, usually represented as 64 symbols comprised of numbers 0–9 and letters A–F. No matter how short or how long the input is – be it a single word (hello) or even a whole novel (Bleak House by Charles Dickens) – the hash is fixed at 64 characters. | ||||||||||
| Are blockchain hashes the same length? | A hash is a mathematical function that converts an input of arbitrary length into an encrypted output of a fixed length. Thus, regardless of the original amount of data or file size involved, its unique hash will always be the same size. | ||||||||||
| How many characters is a blockchain hash? | SHA-256, is a hashing algorithm used to convert text of any length into a fixed-size string of 256 bits (32 bytes). | ||||||||||
| What is the length of blockHash? | Block hash is calculated using the keccak256 algorithm that always results in 32 bytes (64 hex characters prepended by 0x ) no matter the input length. | ||||||||||
| How long can hashes be? | The hashing functions return a 128-bit, 160-bit, 256-bit, or 512-bit hash of the input data, depending on the algorithm selected. An expression that represents the string value to be hashed. | ||||||||||
| How long is a Bitcoin TX hash? | 32 bytes
Transaction Inputs
|
||||||||||
| What is the output produced by a hash algorithm called? | A hash function is a one-way (nonreversable) function that takes an arbitrary plaintext message and creates a fixed size numerical output called a message digest that can be used as a proxy for our original message. | ||||||||||
| What is hash process in blockchain? | A hash function turns an input (for example text) into a string of bytes with a fixed length and structure. The output or value created is called a 'hash value' or 'checksum. ' Any hash value created from data using a specific hashing algorithm is always the same length and one-way - it cannot be reversed. |
- What is hash identifying each block in the blockchain?
- Each block within the blockchain is identified by a hash, generated using the SHA256 cryptographic hash algorithm on the header of the block. Each block also references a previous block, known as the parent block, through the “previous block hash” field in the block header.
- What is hash pointer in blockchain?
- A hash pointer is a tuple that contains a traditional pointer along with the hash of the data element that is being pointed to. It allows us to validate that the information being pointed to has not been modified.
- What is the process of hashing called?
- Hashing is the process of transforming any given key or a string of characters into another value. This is usually represented by a shorter, fixed-length value or key that represents and makes it easier to find or employ the original string. The most popular use for hashing is the implementation of hash tables.
- How many possible SHA 256 hashes are there?
- 2256 possible hash values Collisions are incredibly unlikely: There are 2256 possible hash values when using SHA-256, which makes it nearly impossible for two different documents to coincidentally have the exact same hash value. (More on this in the following section).
- How many possible hash values are there?
- Second, having two messages with the same hash value (called a collision) is extremely unlikely. With 2256 possible hash values (more than the number of atoms in the known universe), the likelihood of two being the same is infinitesimally, unimaginably small.
- How many combinations of hash are there?
- The possible number of unique hashes can be expressed as the number of possible values raised to the number of bits. For SHA-256 there are 2256 possible combinations. So, 2256 combinations.
- How many secure hash algorithms are there?
- The Secure Hash Standard specifies five secure hash algorithms, SHA-1, SHA-224, SHA-256, SHA-384, and SHA-512. All five of the algorithms are iterative, one-way hash functions that can process a message to produce a condensed representation called a message digest.
- Has SHA256 been cracked?
- Bitcoin's SHA256 encryption algorithm is still safe despite Chinese researchers' claims of cracking RSA encryption with existing quantum computers. A group of 24 Chinese researchers said they could factor a 48-bit number using a 10-qubit quantum computer.
- Why is hashing used in blockchain
- May 28, 2023 — A hash is a function that meets the encrypted demands needed to secure information. Hashes are of a fixed length, making it nearly impossible to

